Report
Executive Summary
This investigation focused on the domain rixav.sbs following concerns about its legitimacy and initial access anomalies. Analysis of the site's structure, behavior, and external reputation data indicates it is a high-risk platform with clear indicators of malicious intent. The domain is newly registered with no verifiable history or trust signals. Multiple security intelligence sources flag it with critically low trust scores. Upon visiting the site, users are immediately presented with a wallet connection interface that progressively funnels them toward disclosing sensitive credentials, specifically crypto wallet recovery phrases and private keys. The platform's design, user flow, and technical setup are consistent with Web3 phishing infrastructure. Assessed risk level: High. Any user who interacted with this site and entered wallet credentials should treat those credentials as compromised.
Scam Type Analysis
The website rixav.sbs operates as a Web3 wallet phishing site, specifically targeting cryptocurrency users by impersonating a legitimate wallet recovery or RPC connection service. The attack flow follows a well-documented pattern. Users land on the site under the impression they're resolving a wallet issue, are prompted to select their wallet provider, encounter a staged "connection failure," and are then pushed to manually enter their recovery phrase or private key to "verify" the account. This isn't a bug in the flow, it's the mechanism. The connection failure is deliberate; the credential input is the goal. Branding elements like "RPC Recovery Hub," polished loading animations, and professional-looking wallet selector screens are present specifically to manufacture credibility. There is no actual service here. The entire interface exists to extract seed phrases.
Evidence Analysis
The findings span three categories: technical indicators, behavioral patterns, and external intelligence. On the technical side, the domain is newly registered, a consistent trait in short-lived phishing campaigns designed to operate briefly before being flagged and abandoned. The site routes through Cloudflare, which obscures backend hosting details and complicates attribution. While Cloudflare is used by legitimate sites, it's a standard layer in phishing infrastructure for exactly this reason. Behaviorally, the site's UX is engineered around escalating pressure. The wallet connection interface loads immediately with no context or onboarding. Repeated connection prompts, loading states, and staged failures create urgency and confusion, conditions under which users are more likely to comply with unusual requests like entering a recovery phrase. This staged flow is a hallmark of credential harvesting operations. External intelligence corroborates the on-site findings. Security platforms independently flag rixav.sbs as a phishing domain with trust scores in the critical range. Taken together, a new domain, Cloudflare-masked infrastructure, credential-harvesting UX, and third-party threat flagging all consistently point to a purpose-built phishing site, not a malfunctioning legitimate service.
Correlated IOCs
| Domain | rixav[.]sbs | Confirmed | | URL | hxxps://rixav[.]sbs/sync | Confirmed | | IP Address | 172[.]67[.]134[.]99 | Confirmed |
Recommendations
- Do not interact further with rixav.sbs using real accounts, wallets, or credentials
- Any wallet credentials, especially recovery phrases, entered on the site should be considered compromised. Migrate assets immediately if applicable
- All further investigation should be conducted in a sandboxed or isolated environment with burner accounts only
- Submit the domain to security platforms (VirusTotal, PhishTank, Google Safe Browsing) for broader flagging.
- Watch for domain variants and typosquats that may be part of the same campaign infrastructure
Findings
Initial Entry Point for Credential Harvesting
mediumThe wallet connection interface serves as the primary entry point into the platform’s interaction flow. The site cannot be accessed unless your wallet is connected! By presenting a familiar Web3-style interface, the site mimics legitimate decentralized applications to build initial trust with users. This design choice reduces suspicion and encourages engagement, especially for users who are accustomed to connecting wallets on legitimate platforms. This step is critical in the phishing process, as it sets up the user to proceed further into the workflow where more sensitive information is requested.
Direct Credential Harvesting Mechanism
mediumThe request for recovery phrases or private keys is a strong indicator of malicious intent and aligns directly with known phishing behaviors in cryptocurrency scams. Legitimate platforms never request this level of sensitive information, as recovery phrases provide complete control over a user’s wallet. By prompting users to input this data, the platform is likely attempting to capture credentials that can be used to immediately access and drain funds. This represents a direct and high-risk threat to users interacting with the site.
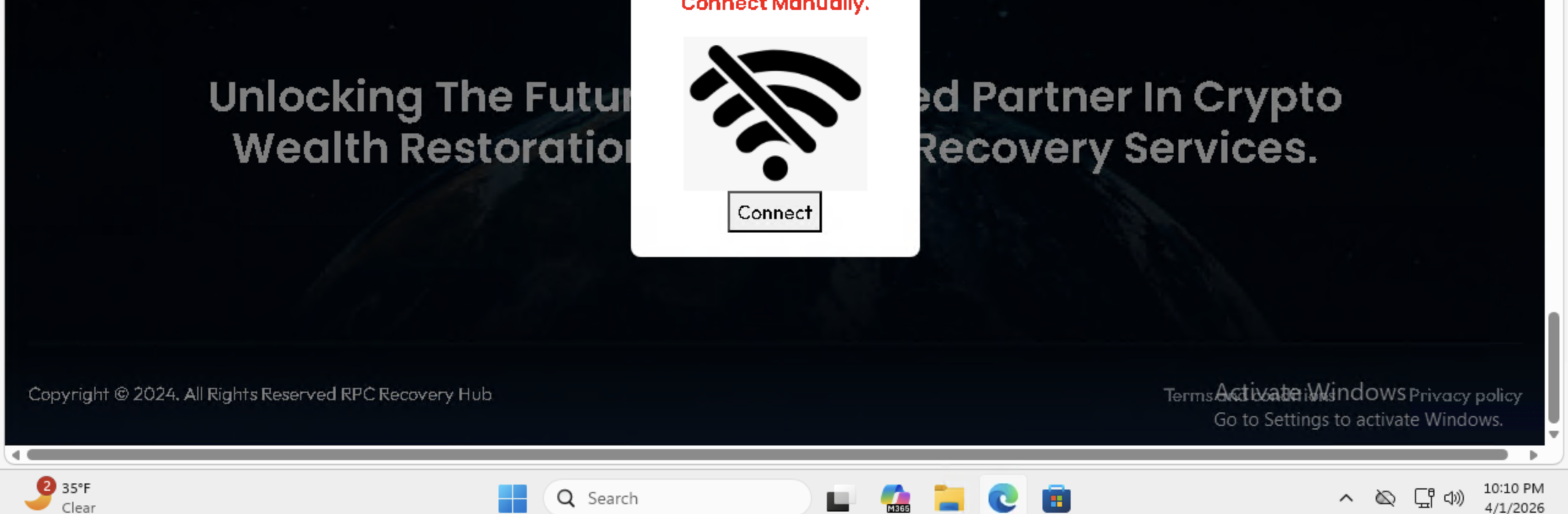
Forced Escalation to Manual Input
mediumThe “Failed to Connect” message appears to function as a manipulation tactic rather than a legitimate system error. By simulating a failed wallet connection, the platform creates a sense of urgency and inconvenience, pushing users toward alternative methods such as manually entering sensitive credentials. This escalation strategy is commonly used in phishing schemes to bypass safer authentication methods and guide users into submitting information that can be exploited.
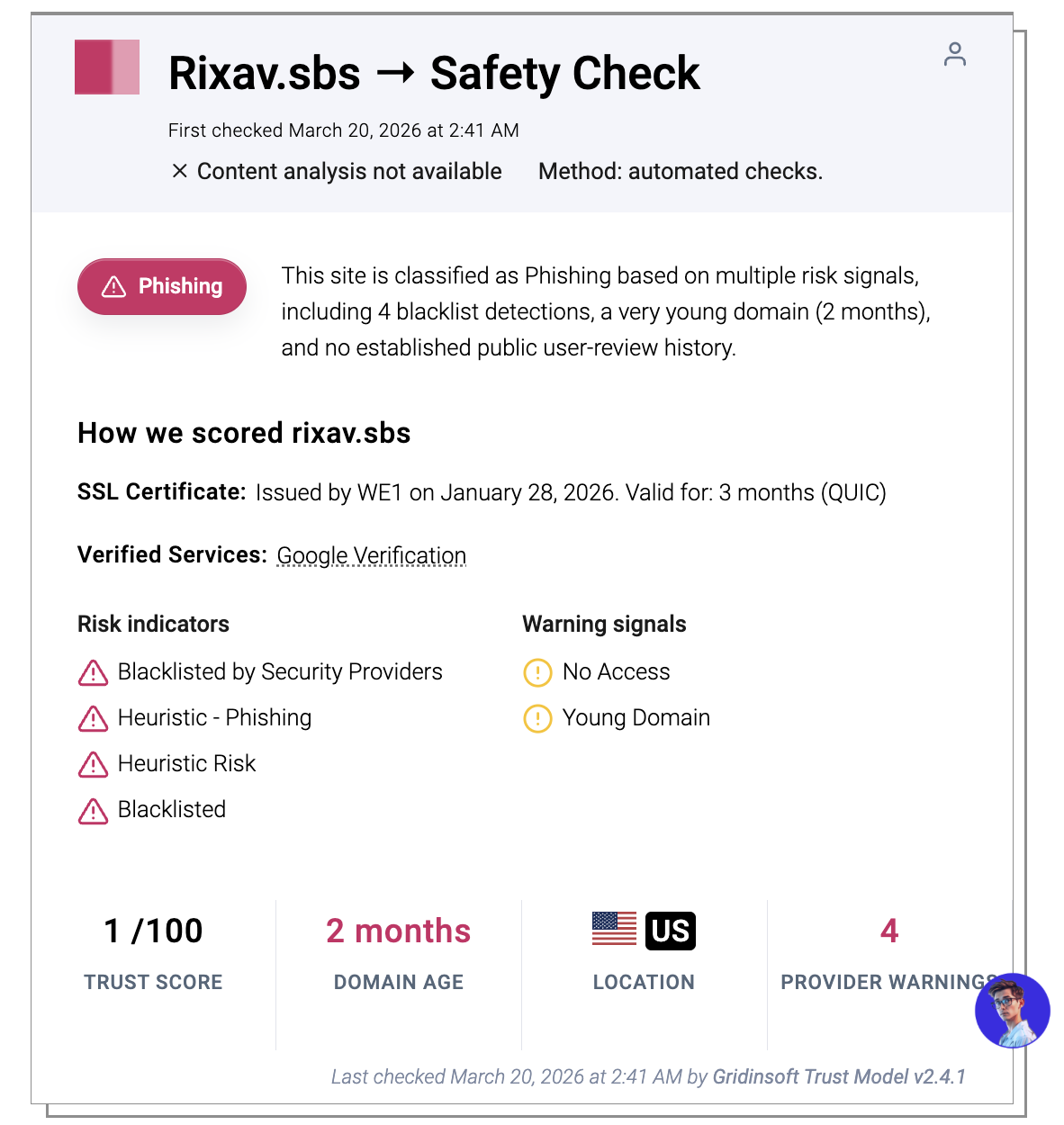
External Validation of Malicious Activity
highThe presence of a browser-level security warning provides strong external validation that the site has already been flagged as unsafe by security providers. These warnings are typically based on aggregated threat intelligence, user reports, and automated detection systems. This indicates that the domain is not only suspicious from an internal analysis perspective, but has also been recognized as potentially harmful across broader cybersecurity networks.
High-Risk Infrastructure Indicators
mediumThe domain characteristics strongly align with patterns commonly associated with malicious or short-lived phishing operations. Newly registered domains often lack historical reputation, making them ideal for attackers to deploy scams quickly before detection systems fully respond. The extremely low trust score and presence on multiple blacklists further reinforce the likelihood that this domain is part of a coordinated malicious campaign rather than a legitimate service.
Impersonation and Deceptive Branding
mediumThe mismatch between the platform name and the domain suggests intentional impersonation or deceptive branding. This tactic is frequently used in phishing campaigns to create the appearance of legitimacy while avoiding direct association with known or verifiable entities. By using a generic or misleading brand name, the platform attempts to gain user trust without providing any verifiable organizational identity.
Evidence
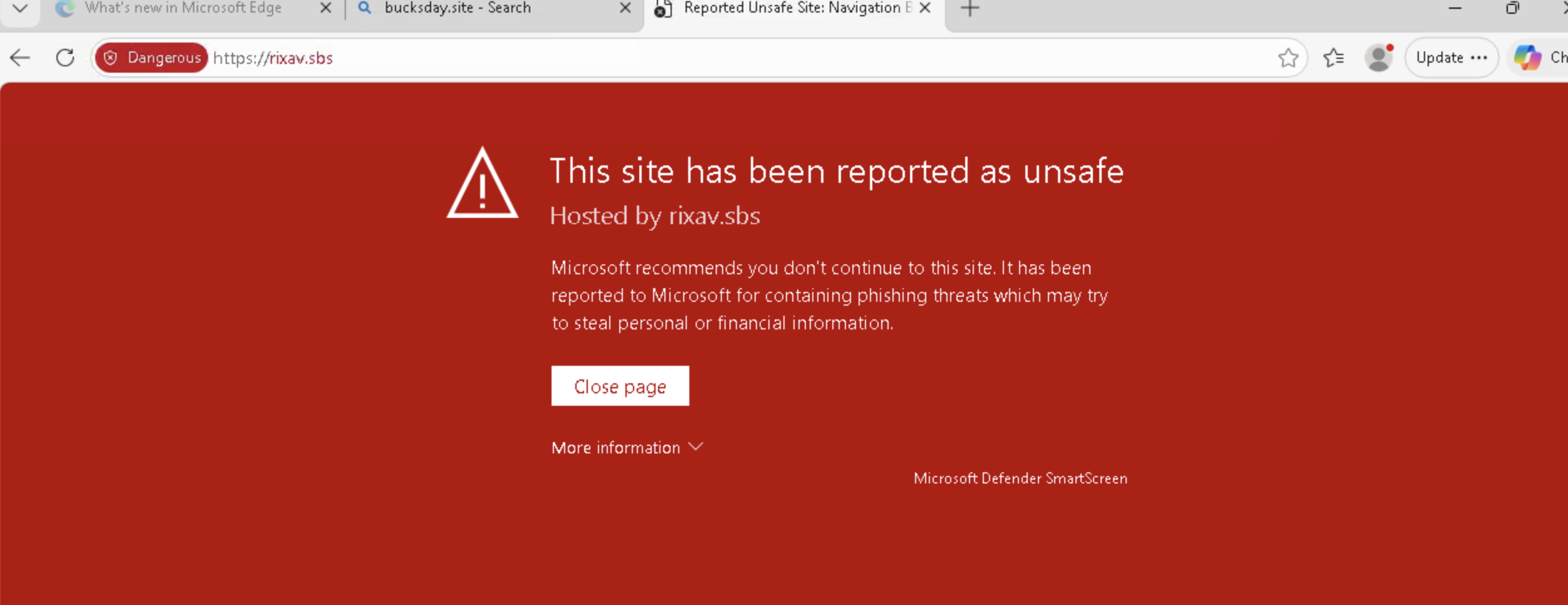
Browser SmartScreen Warning
The browser displays a security warning indicating that the site may be unsafe or involved in phishing.

“Failed to Connect” Prompt
After attempting a connection, the platform displays a “Failed to Connect” message and prompts users to try alternative connection methods.
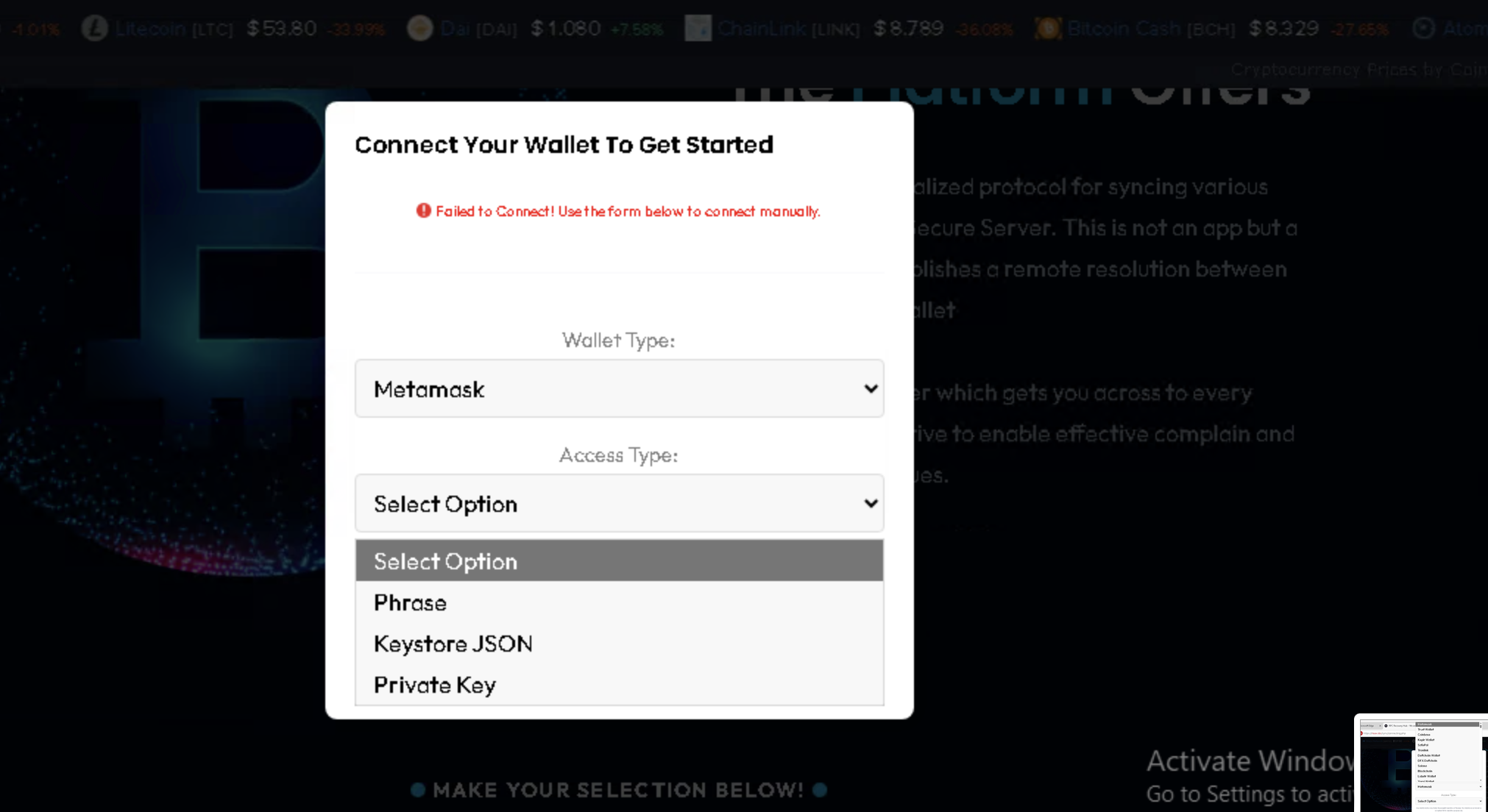
Recovery Phrase / Private Key Input Fields
The platform provides input fields asking users to manually enter recovery phrases, private keys, or keystore JSON files.
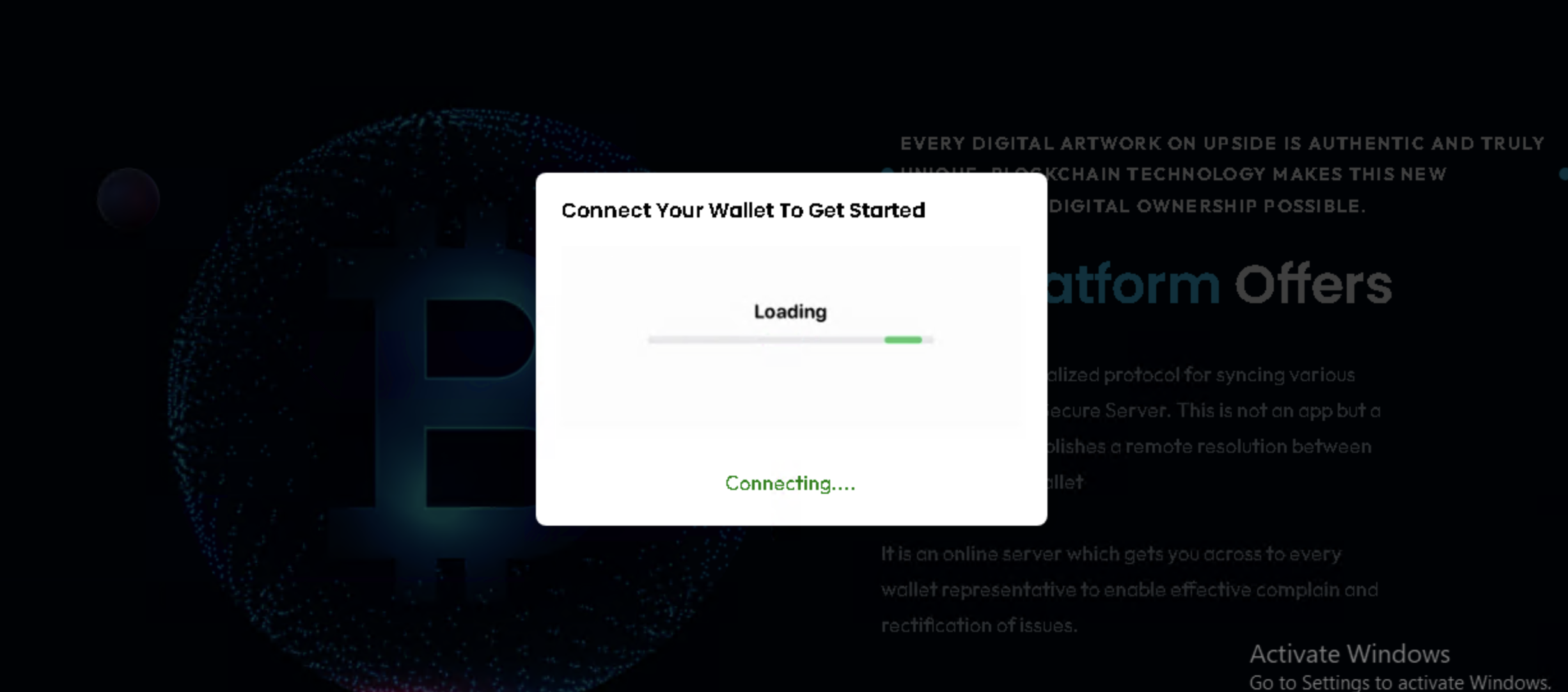
Wallet Connection Interface
The platform presents a “Connect Your Wallet” interface prompting users to connect a cryptocurrency wallet in order to proceed.
Correlated IOCs
| Type | Value | Status |
|---|---|---|
| IP Address | 172[.]67[.]134[.]99 | Confirmed |
| URL | hxxps://rixav[.]sbs/sync | Confirmed |
Stay Protected
Use our free tools to protect yourself from the threats discussed in this investigation.